Since at least 2009—when the Arab Spring illustrated the possibilities, and the vulnerabilities, of online democracy and human rights activism—digital security trainers and experts have aided human rights activists in repressive or otherwise dangerous environments around the world. Much of this global work has been supported by large foundations and state agencies, but in the United States, the philanthropy community is still catching up to the digital security needs faced by civil society. The result is that, even when an organization readies itself to improve the security of its data infrastructure, it seldom has the resources to do so in any meaningful way.
And yet, over the last two years—heating up after the 2016 US presidential election—the need to support US civil society’s response to online threats has increased significantly.
While many communities have faced government surveillance and analog hacking attempts for years (think the FBI and Martin Luther King, Jr., or every generation’s attacks on democracy activists and whistleblowers), threats to the data security of the nonprofit sector are broader and arguably graver than ever before. The Immigration and Customs Enforcement (ICE) agency is gaining access to surveillance tools previously restricted to law enforcement. Hackers attempted to derail Net Neutrality advocacy via a sophisticated phishing attack. The director of a Mexican anti-corruption group was targeted with government-sponsored spyware. Thousands of organizations store sensitive user data in insecure databases that can be easily hacked to reveal the giving information of anonymous donors or vice versa, with partisan attacks on donors leading to risks to their grantees and their missions.
The excellent guides, trainings, and webinars explaining the need for encrypted messaging services, secure email, and protected social media accounts are essential. But the reality is that blog posts on using Signal, massive guides to protecting your digital privacy, and broad statements like “use Tor” can be hard to understand or act on. Meanwhile, it’s nearly impossible for service-oriented organizations operating across the far reaches of the philanthropic universe to identify and connect with qualified digital security experts who understand their specific contexts and challenges.
No one is to blame for this gap. Existing digital security resources are usually designed to help individuals identify the tools they need to secure their personal digital footprint, or to respond to emergencies and critical threats as they are happening. It’s much harder and more resource-intensive to teach entire organizations—and their funders—how to take a long view of digital attitudes and habits, or to analyze the use, retention, and sharing of sensitive user, organizational, and mission-focused data.
This is why, in this age of increasingly sophisticated attacks against civil society’s digital infrastructure, we need the philanthropic community to support larger efforts in capacity building at the organizational level.
No matter whether an organization houses 5, 50, or 500 staff, changing habits and retrofitting old systems and policies is difficult and expensive. Retrofitting funders’ traditional ways of thinking takes work too. Based on our experience addressing digital security needs and making the big changes necessary to protect themselves online, here are four steps civil society organizations and their funders can take to begin addressing this urgent need.
1. Commit to digital security as essential to all work.
The Equifax breach and the Russian interference in US elections are massive reminders that online data is vulnerable to attacks from all quarters. Many funders and civil society organizations know they need to take action, but they don’t know how to do it or who can help. And as civil society begins to notice these gaps, it is important to observe that digital security work takes resources, energy, and focus. Like fiscal responsibility and strong governance, a digital security strategy should be part of any organization’s strategic planning.
2. Take big responsibility for big data.
The conversation around what researcher Lucy Bernholz calls “digital civil society”—mission-based work conducted online, with all of the attendant benefits and pitfalls—is largely about the growing mountains of data organizations create every day that, like Styrofoam, never disappear. That data—including personally identifiable information such as names, phone numbers, and email and mailing addresses—has great value not only to well-intentioned civil society organizations, but also to third-parties who may wish to use these datasets to surveil individuals or communities, or gain access to private information. Individuals or organizations wanting to debunk #MeToo efforts or target immigrants often attempt to identify individuals accessing organizations’ online services or social media accounts. One result of the recent Cambridge Analytica scandal has been a growing awareness of the ways federal agencies can access seemingly “private” Facebook data to build cases against individuals, including undocumented immigrants, or those in power can wield data to increase their stranglehold over public life.
To say the least, the need to secure both an organizations’ own assets and those it trusts to third-parties puts a huge amount of pressure on civil society to improve its security services—a job it is currently ill-equipped to manage. Nevertheless, more organizations need to take the responsibility of stewarding their data seriously. If they don’t, they put millions of the people they serve, engaged supporters, and entire institutions at risk.
3. Prioritize “capacity building.”
Organizations often respond to perceived digital security threats or actual attacks by bringing in a security trainer and/or holding webinars on the basics or on whole new strategies. While this is often the “lowest hanging fruit” when it comes to incident response, all too often trainings and webinars simply aren’t enough. The drawbacks of this “quick fix” are that, as the digital and political world changes and the field of digital security grows, new threats emerge, and the risks to organizations small and large are continually shifting. The hardware, software, bandwidth, and budget constraints of a given group mean that simply training individuals, without taking a systemic approach to an organization’s overall security, makes it much harder to address moving targets like network vulnerabilities, policies governing the sharing of personal data at border-crossings, or online surveillance.
Instead, we all need to engage in a growing conversation around capacity building: addressing the structural vulnerabilities that make it easy for an online adversary to attack your organization. It takes time, but we can all do this by thinking about digital security as a capacity-building effort with a multi-stage process, including: 1) coming to a holistic understanding of your organizations’ “threat model”—the adversaries you face, the data they might want, and your vulnerabilities in the face of an attack; 2) auditing the specific systems your organization uses to store, share, and process user data, as well as the communications platforms, networks, and devices staff and constituents use; and 3) developing strategies for addressing vulnerabilities from the ground up, rather than piecemeal through trainings or one-off fixes.
We all have to start somewhere. Funders, ask your grantees about how they can better address digital security. Nonprofits and grantee groups, include digital security plans in your pitches and proposals. Everyone, start or continue to engage in the dialogue about what is at risk whenever you can, through reading and engaging with organizations ready and waiting to support, advise, and collaborate with you in this new horizon.
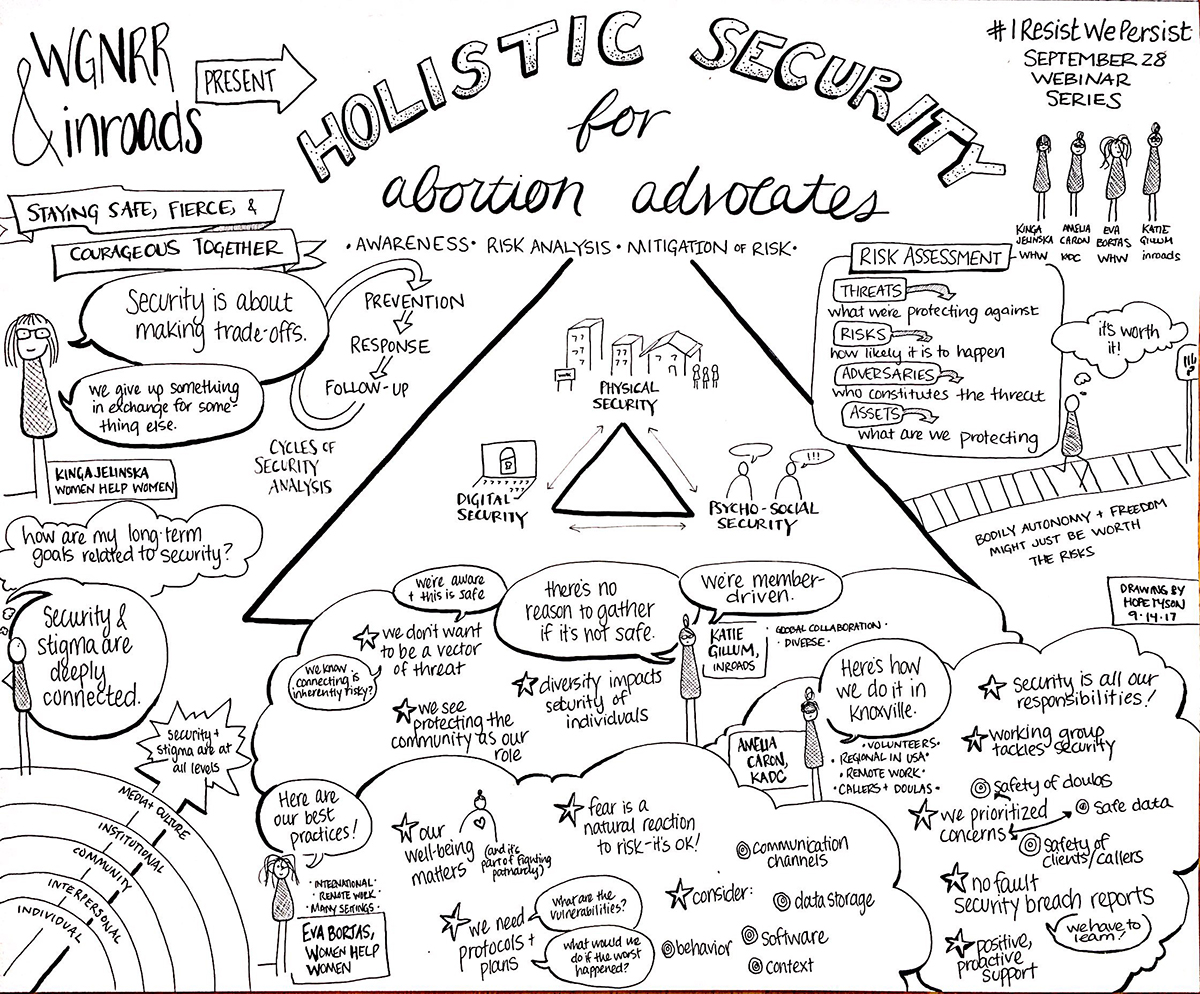 A webinar hosted by inroads and Women’s Global Network for Reproductive Rights to observe International Day for Safe and Legal Abortion included looking at how to expand digital security practices to involve the entire abortion advocacy community and deal with the field’s specific risks. (Illustration courtesy of inroads, Hope Tyson 2017)
A webinar hosted by inroads and Women’s Global Network for Reproductive Rights to observe International Day for Safe and Legal Abortion included looking at how to expand digital security practices to involve the entire abortion advocacy community and deal with the field’s specific risks. (Illustration courtesy of inroads, Hope Tyson 2017)
4. See the shared threat as a call for interdependence.
Ultimately, as we take the steps above, we need to shift our thinking to prioritize digital security as a shared, communal responsibility, rather than an individual responsibility or something that only high-risk groups shoulder. The beauty of digital communication and services is that they can help us connect, cut costs, and provide services in ways we couldn’t dream of in past generations. But it also means we are deeply interdependent. Whether a global NGO, local service organization, or national foundation, threats to our data, sources of support, or communities on the ground affect us all. Consider a simple breach of cloud-based email servers that leads to the release of information about donors, grantees, or at-risk populations.
In many instances, organizations and movements working on racial equity, abortion, immigration, trans health, and domestic violence are making great strides. For example, the Center for Media Justice and May First/People Link recently launched Defend our Movements, a “digital self-defense knowledgebase” that addresses the specific threats faced by communities of color. The National Network to End Domestic Violence’s Safety Net project is focused on staying ahead of the many security challenges survivors of domestic violence face. Many other organizations and networks hold hard-won expertise in their ranks, but if their partners and donors don’t commit to addressing their own risks, the community and trust civil society needs to deal with digital security will be difficult to build.
None of us wants to be a risk vector for ourselves, our partners, funders, or those we serve. To prevent that, we need to be realistic about our interdependence, and work together to protect our intersecting communities from the threats that this connection and progress can create.
Read more stories by Josh Levy & Katie Gillum.